News
- Report
"SQL injection" increased by 150% year-on-year ~Announcement of "Cyber-attack detection report targeting web applications" for January-March 2023~
Cyber Security Cloud Co., Ltd. (Headquarters: Shinagawa-ku, Tokyo, Representative Director, President and CEO: Toshihiro Koike, hereinafter “our company”), a global security manufacturer that develops anti-hacker services will announce the "Cyber-attack detection report targeting web applications (hereinafter referred to as "this report")" for from January 1 to March 31, 2023.
This report aggregate, analyze and calculate the cyber attack logs observed by our Cloud-based WAF, “Shadankun,” which visualizes and blocks cyber-attacks on web applications, and by “WafCharm,” an automated operation service for public cloud WAFs.
《 Report Summary 》
・ The number of cyber-attacks has shown a slight upward trend since the end of the previous fiscal year.
・ “SQL injection” increased by 150% year-on-year.
・ “Brute Force Attack” also increased by 66% year-on-year.
■ Cyber attack detection status from January to March 2023
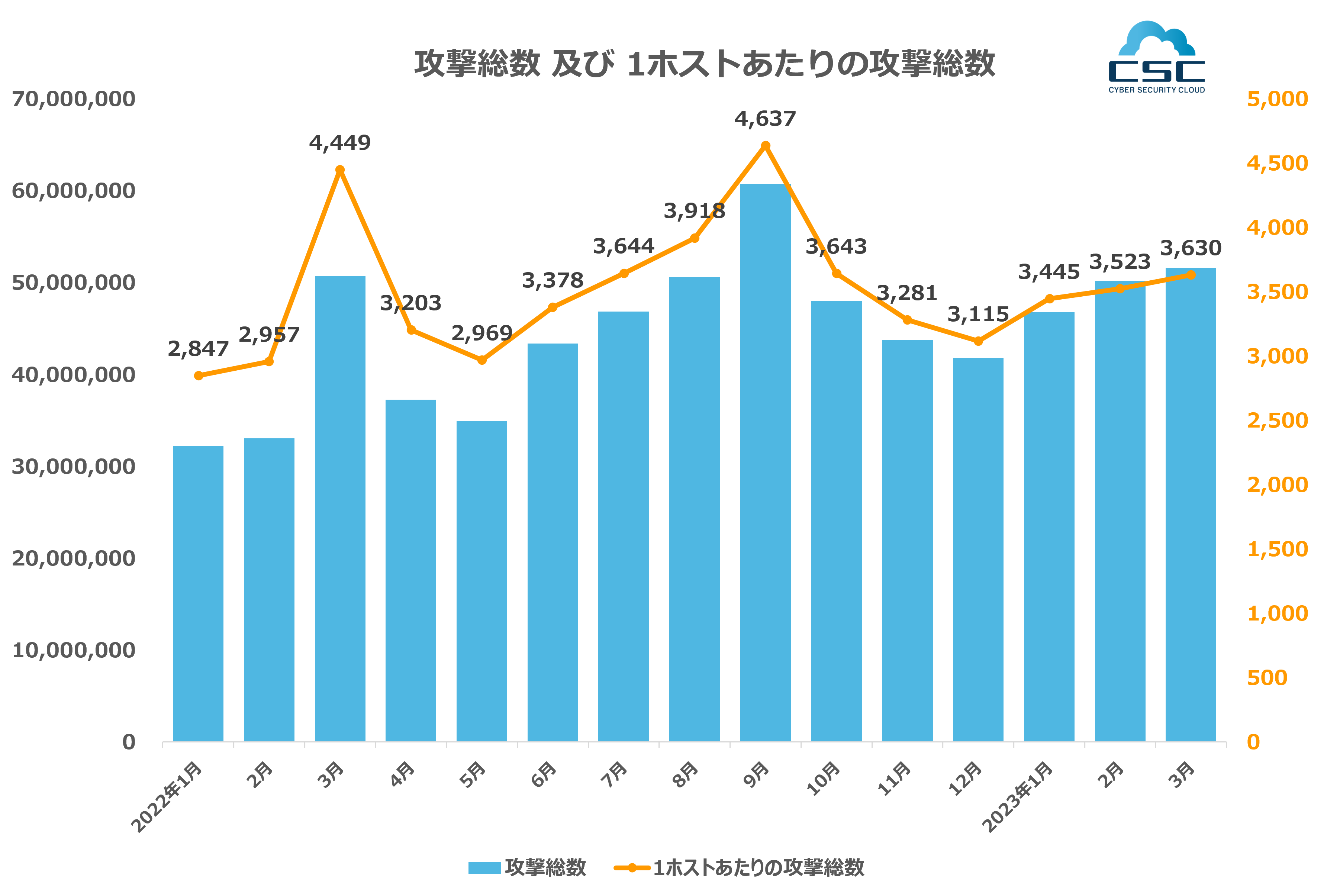
From January 1, 2023 to March 31, 2023, the total number of cyber-attacks on web applications detected by our company was 148,631,502, and 10,598 per host (*).
Also, although the number of attacks increased month by month this time around, it remained at a moderate pace.
* Calculated using the total number of protected hosts of Shadankun" (Web type: number of FQDNs, server type: number of IPs) and the number of protected hosts of "WafCharm" (WebACL) as the denominator.
■ Detection status by attack type
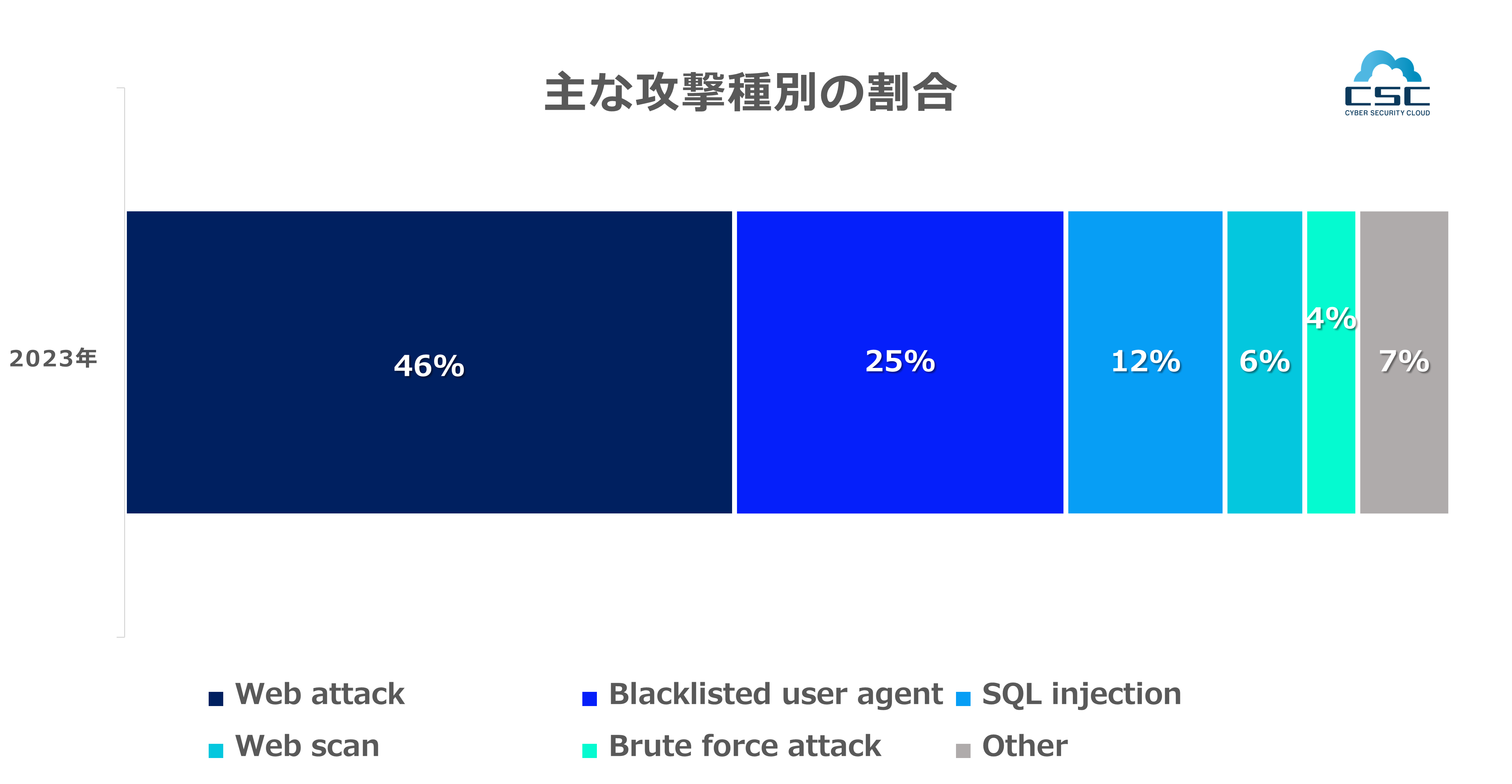
Categorizing the cyberattacks detected by our company by attack type, we can see that from January to March 2023, there were approximately 69 million "web attacks," which are attacks against vulnerabilities in the software that makes up web servers, accounting for 46% of the total. occupies. Next, "Blacklisted user agent", which is an attack by a bot using a vulnerability scanning tool, etc., is about 37 million, accounting for 25%. In addition, "SQL injection," which intentionally targets system vulnerabilities and executes unexpected SQL statements to manipulate database systems illegally, accounted for approximately 17 million cases, or 12%.
■ Among the attack types to watch out for, "SQL injection": +150% year-on-year increase
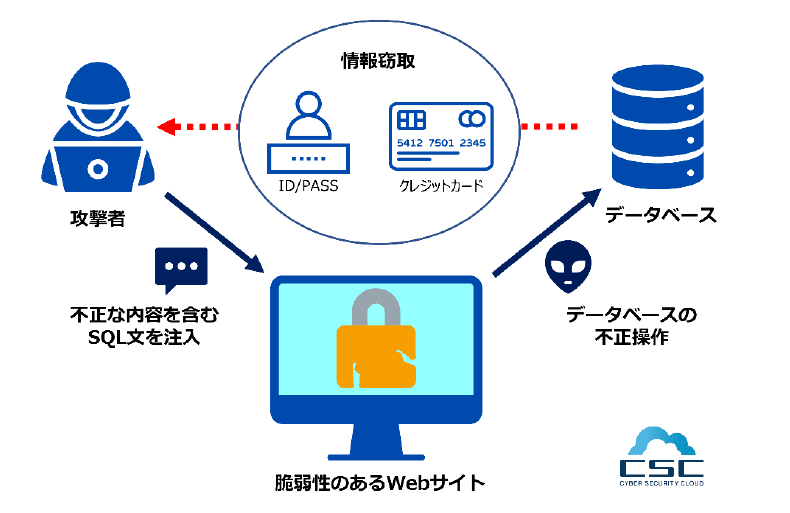
SQL injection is an attack that exploits vulnerabilities (incompleteness and fragility) of websites, etc., and illegally creates "SQL statements (instructions that move database information)" into requests to the database. It is an attack that manipulates the database illegally by "injection".
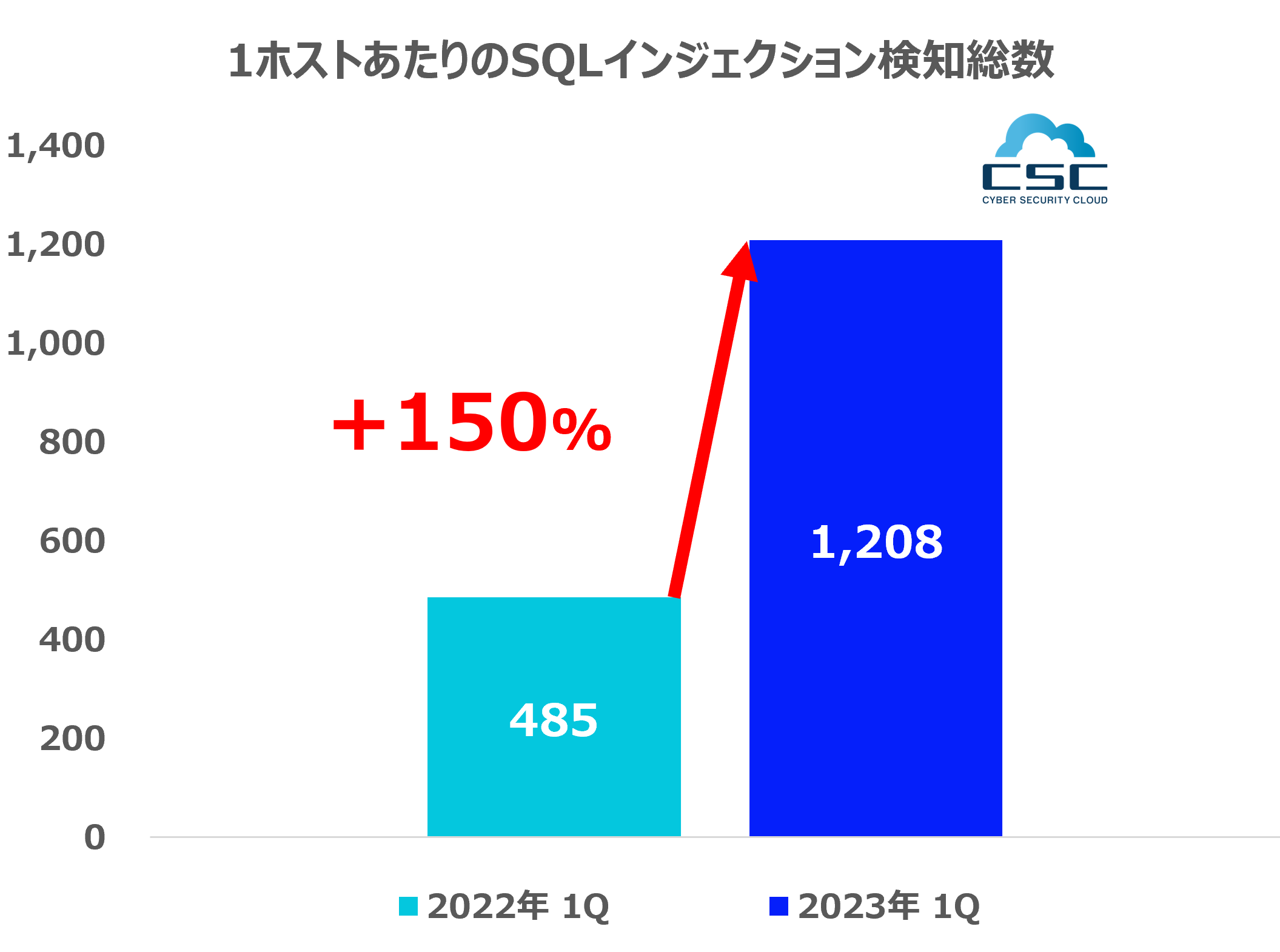
Compared to January to March 2022, the total number of SQL injection attacks in January to March 2023 increased from 5,481,900 to 16,985,151, an increase of approximately 210% (approximately 11.5 million cases). Cases per host increased from 485 to 1,208, an increase of approximately 150% year-on-year.
There are several reasons why SQL injections are increasing year by year.
◆ Easy to carry out cyberattacks
SQL Injection can be attacked by simply injecting a simple script into a web form.
◆ Increase in web application vulnerabilities
With the spread of web services such as e-commerce sites, vulnerabilities to SQL injection are also increasing. One of the reasons is that various functions have been added to the web application itself, and the website has become complicated due to the use of multiple systems.
◆ Neglecting vulnerabilities due to unapplied security patches
Due to concerns about business impact and lack of cybersecurity awareness, software with reported vulnerabilities is left unupdated and likely to be exploited.
■ The next thing to watch out for is "Brute Force Attack": +66% YoY increase
Brute force attack is one of the methods of cracking passwords by "brute force attack".
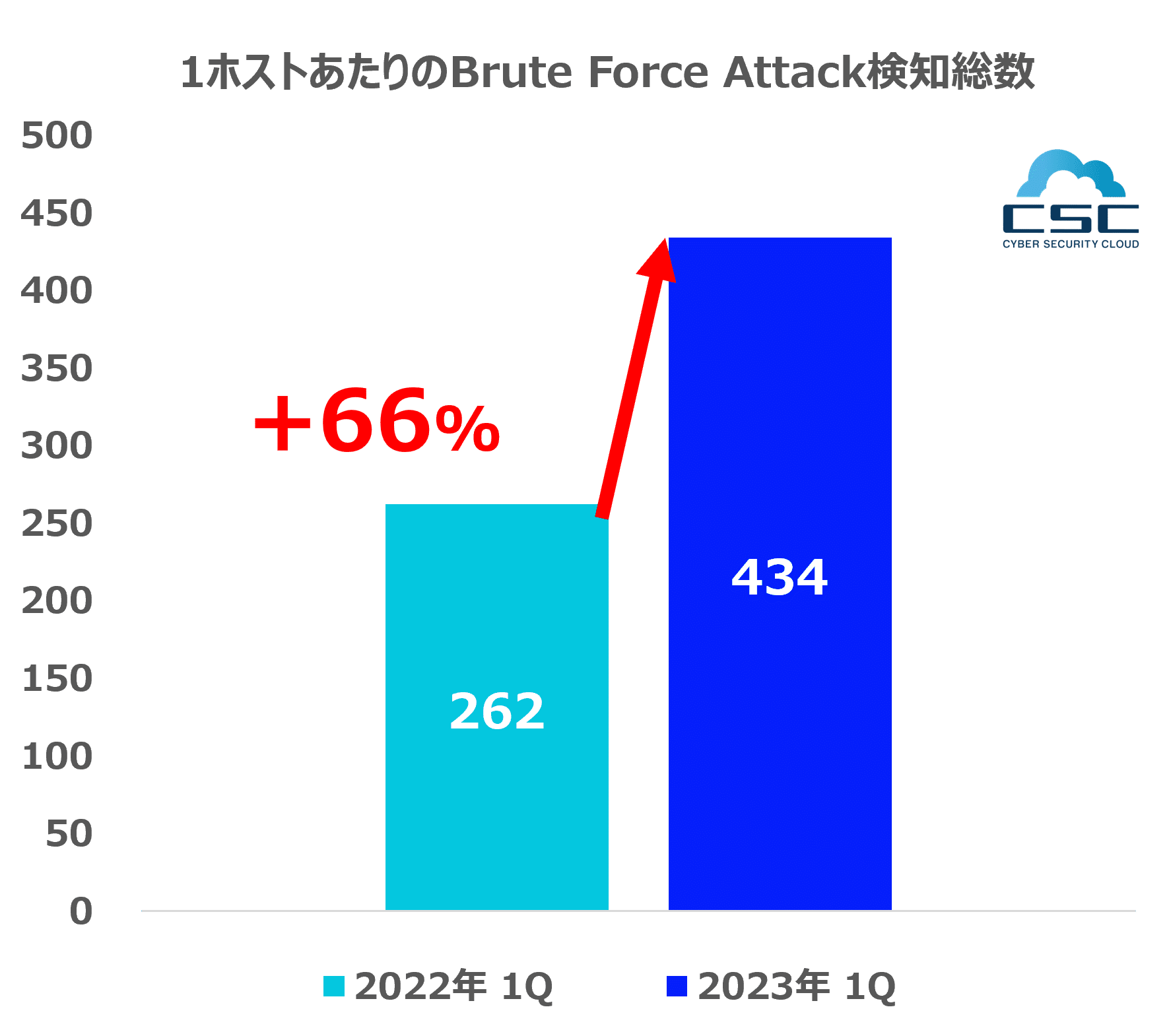
Compared to January to March 2022, the total number of brute force attacks in January to March 2023 increased from 2,950,044 to 6,074,706, an increase of approximately +206% (approximately 3.12 million cases). Cases per host increased from 262 to 434, an increase of 66% YoY.
Also, the reasons for the increase in brute force attacks include:
◆ Use of weak passwords by users
Many people use weak passwords (short, predictable, reusing the same password). From this current situation, brute force attacks have become cyberattacks with a high success rate.
◆ Utilization of huge computing resources in the cloud environment
By using faster and more powerful computers, attackers can try more passwords in less time than before.
In particular, the rise of cloud computing has made it possible to easily use enormous computational resources, which has greatly influenced the increase in brute force attacks.
◆ Exploitation of automated tools and botnets
By exploiting automation tools and botnets, attackers can automatically generate a large number of login attempts.
These tools are widely available on the Internet and are contributing to the increase in brute force attacks.
◆ Frequent password information leaks
Large-scale data breaches are frequent, and leaked account information (username/password) is used for brute force attacks.
These accounts are exposed on the dark web as "dictionary data" for further attacks.
◆ Inadequate security measures
Many systems and websites do not have proper cybersecurity measures and are inadequately protected against brute force attacks.
For example, if you do not take appropriate measures such as temporarily locking the target account when a large number of login failures are seen.
■ About Cyber Security Cloud, Inc.
Location: JR Tokyu Meguro Building 13F, 3-1-1 Kamiosaki, Shinagawa-ku, Tokyo
Representative: Toshihiro Koike Representative Director, President and CEO
Established: August 2010
URL: https://www.cscloud.co.jp
Cyber Security Cloud has a management philosophy of "creating a safe and secure cyber space for people around the world", and utilizes world-class cyber threat intelligence and AI technology to provide web application security services and vulnerability information collection.・We provide anti-hacker services such as management tools. We will continue to contribute to the promotion of the information revolution as one of the leading global companies in cyber security, with a focus on WAF.
■ Survey overview
・ Survey period: January 1, 2023 to March 31, 2023
・Survey target: User accounts using “Shadankun” and “WafCharm”
・Investigation method: Analysis of cyber attack logs observed by “Shadankun” and “WafCharm”
