In-house security
Protect your computer and company network
Corporate cybersecurity measures can be divided into "internal security" and "web security."
Unlike internal security measures such as antivirus software and firewalls for PCs, security measures to protect websites are often inadequate, and in recent years, numerous incidents of personal information leaks have occurred.
In particular, the increasing diversity of attack methods utilizing AI-generated content has made web security more important than ever before.
Based on the knowledge accumulated on the front lines of attacks, CSC provides services that can be implemented regardless of company size or technical skill level.

Protect your computer and company network

Protect websites that everyone visits

A service that automatically manages Web Application Firewalls (WAFs) provided by AWS, Azure, and Google Cloud.
A rule set specifically for AWS WAF, available for purchase from the AWS Marketplace. We are one of only eight certified AWS WAF managed rule sellers worldwide, and our services are currently available in over 100 countries and regions.

This service leverages cloud-native security services and provides comprehensive support for the entire operational process from security experts.

Our flagship Cloud-based WAF that visualizes and blocks cyberattacks on websites and web servers.

A service that automatically manages Web Application Firewalls (WAFs) provided by AWS, Azure, and Google Cloud.

This service leverages cloud-native security services and provides comprehensive support for the entire operational process from security experts.
A rule set specifically for AWS WAF, available for purchase from the AWS Marketplace. We are one of only eight certified AWS WAF managed rule sellers worldwide, and our services are currently available in over 100 countries and regions.

A service that collects OS and application vulnerability information from all over the world and provides patch information and workarounds in Japanese along with risks. It is also possible to automate operations (SOAR), such as issuing tickets under predetermined conditions for vulnerabilities in IT assets.
We provide comprehensive vulnerability assessments for vulnerability countermeasures of web applications, platforms, and API. With over 25 years of experience and know-how, we provide hybrid assessments by security experts and tools.

Webtru automates privacy compliance. From current status confirmation to analysis, compliance with regulations is completed automatically. No need for tedious manual checks.

Protect your personal information by using an email address created with Bunsin. Block spam emails immediately and receive only the emails you need.
A technology company that creates new value through security and system development. Supports cloud construction and application development based on CSC's know-how.

Software for protecting Web APIs is released as OSS. A plugin that adds security features to the API gateway Kong.
Cyber Security Cloud responds to ever-evolving cyber-attacks by developing cutting-edge AI technology and utilizing world-class threat intelligence.
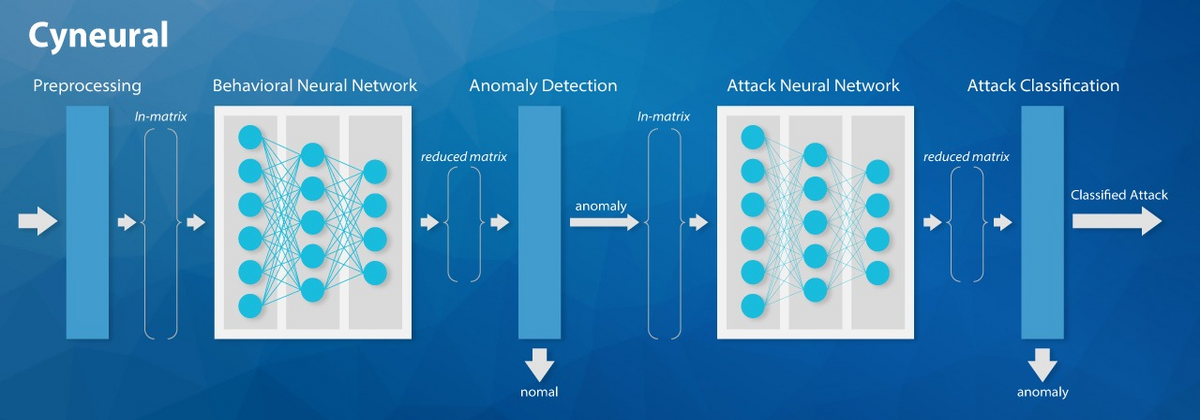
Cyneural, an attack detection AI engine that uses deep learning, uses a feature extraction engine that utilizes knowledge cultivated through research on web access and many attack methods. By building multiple types of learning models in the engine, we can quickly detect not only general attacks, but also unknown attacks and false positives.
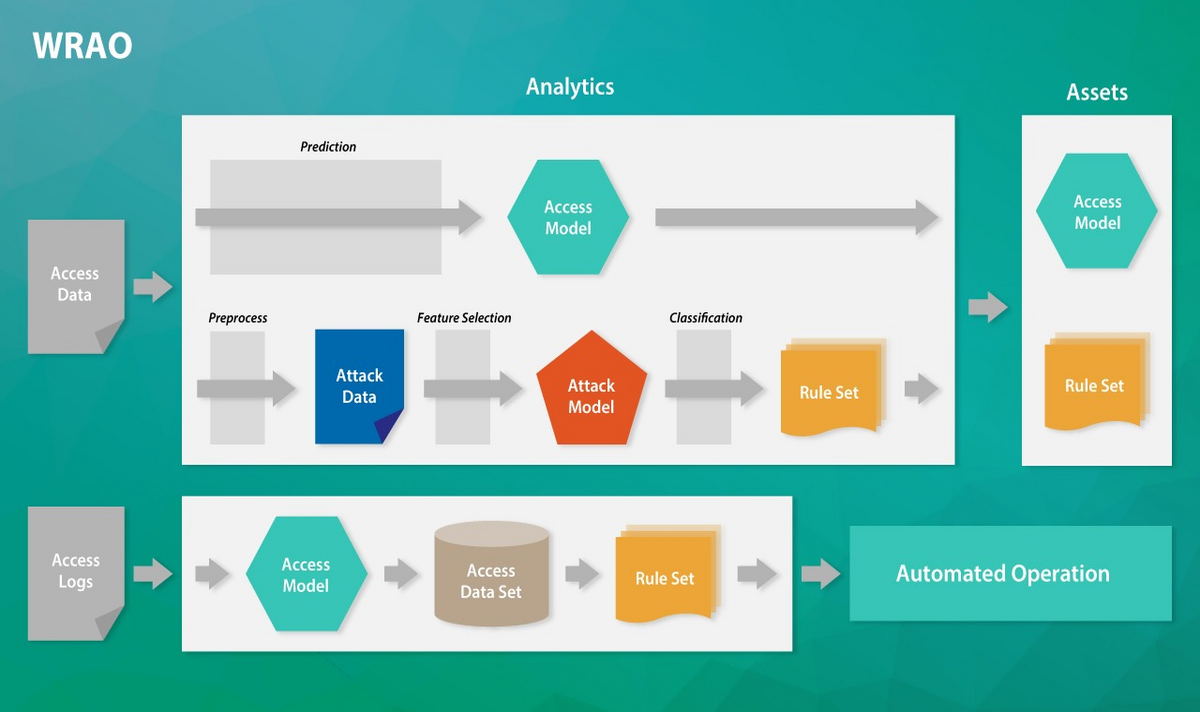
We have developed WRAO, a technology for automatic operation of rules for websites (patented), to reduce the cost of WAF rule operation. WRAO learns website access trends from users' web access data and predicts the characteristics of attacks on those websites. This enables automatic selection of flexible rules that match the modeled web application and attack model.
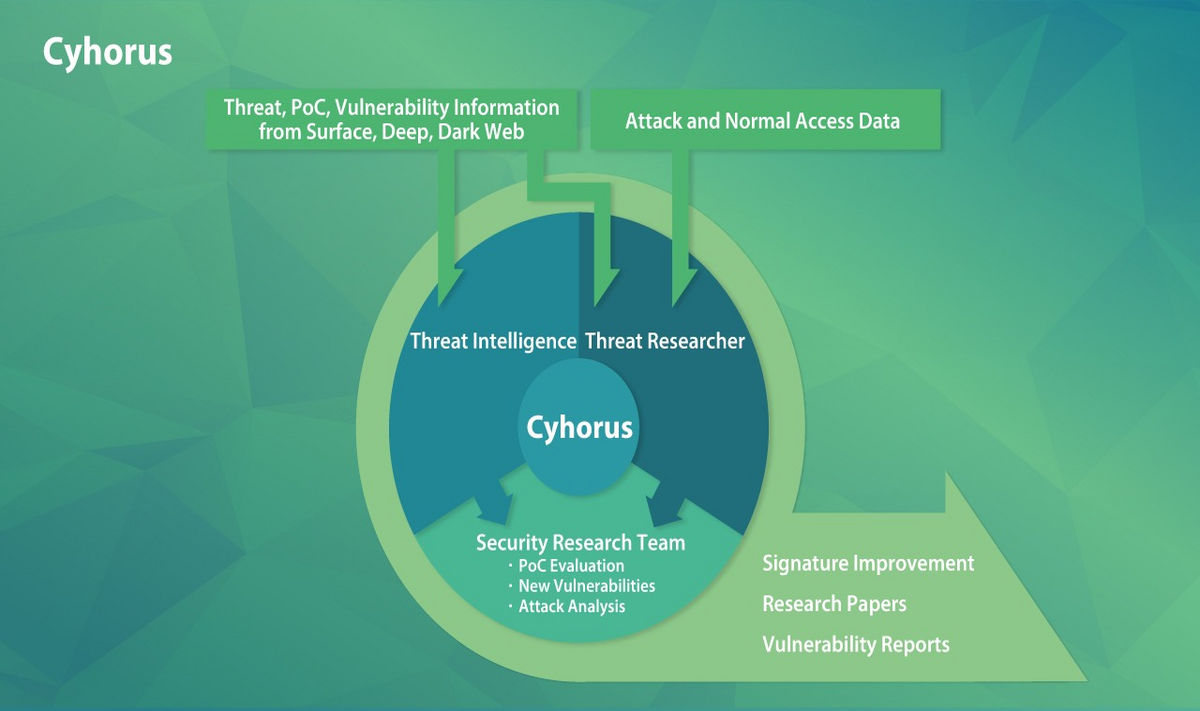
Demands for collection and evaluation of cyber threat information and speed of reflection in signatures are increasing day by day. Cyhorus is a team organized by our elite, and has partnered with an Israeli company that possesses world-class cyber threat intelligence information. We consistently carry out accurate evaluation and signature creation.