ニュース
グローバルセキュリティメーカーの株式会社サイバーセキュリティクラウド(本社:東京都品川区、代表取締役社長 兼 CEO:小池敏弘、以下「当社」)は、2025年4月1日~6月30日を対象とした『Webアプリケーションへのサイバー攻撃検知レポート(以下「本レポート」)』を発表します。本レポートは、当社が提供するWebアプリケーションへのサイバー攻撃を可視化・遮断するクラウド型WAFの『攻撃遮断くん』、及びパブリッククラウドWAFの自動運用サービス『WafCharm(ワフチャーム)』で観測したサイバー攻撃ログを集約し、分析・算出しています。
■ 全体概要:3カ月で5億件超の攻撃ログ
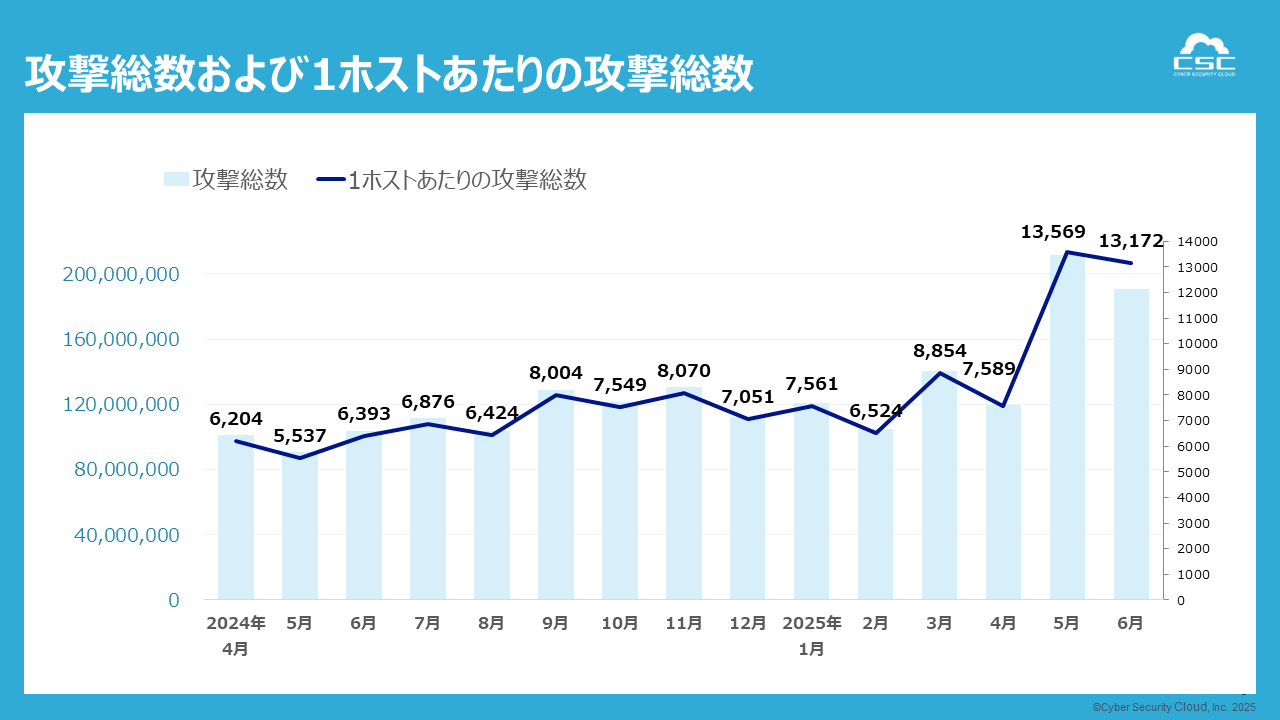
2025年4月1日〜6月30日までに、当社で検知したWebアプリケーションへのサイバー攻撃の総攻撃数は5億2654万件(約67回/秒)にのぼり、前年同期比で78%増を記録しました。
さらに、1ホスト(※1)あたりの攻撃件数は前年比で約2倍に。
(※1) 『攻撃遮断くん』の保護対象ホスト数(Webタイプ:FQDN数、サーバタイプ:IP数)と、『WafCharm』の保護対象ホスト数(WebACL)との総数を分母に概算。
■ 攻撃種別の割合
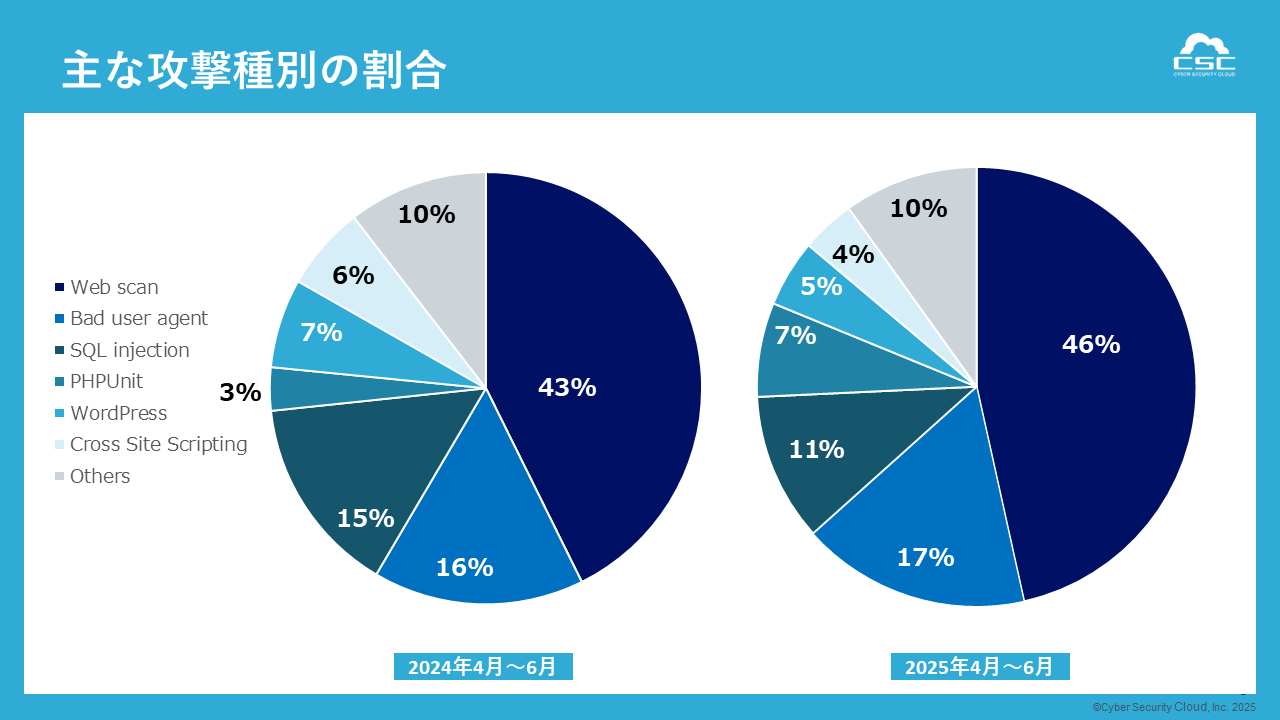
今回の調査期間における主な攻撃種別の傾向を見ると、総攻撃数は増加しましたが、種別構成に大きな変化は見られません。
本レポートでは、SQLインジェクション(SQLi)やクロスサイトスクリプティング(XSS)など、いわゆる「従来型のWebアプリケーション攻撃」が引き続き高頻度で観測されました。これらの攻撃手法は古典的である一方、攻撃の自動化や大規模化が進行しており、検知件数ベースでは過去最高水準に達しています。入力値の検証が不十分なWebアプリケーションや、設定ミス・アクセス制御の不備といった構成上の問題は、セキュリティホールとなるリスクがあり、攻撃の足掛かりとなる可能性があります。
さらに、WordPressやPHPUnitなどのオープンソースソフトウェア(OSS)やCMSに内在する既知の脆弱性を狙った攻撃も多数確認されました。これらのソフトウェアは企業・自治体・個人を問わず広く利用されており、「誤った設定不備や脆弱性」が放置されたままになっているWeb資産が、攻撃者の格好の標的となっていると考えられます。
■ API時代の新定番:Server Side Request Forgeryが約293万件と3倍に増加。
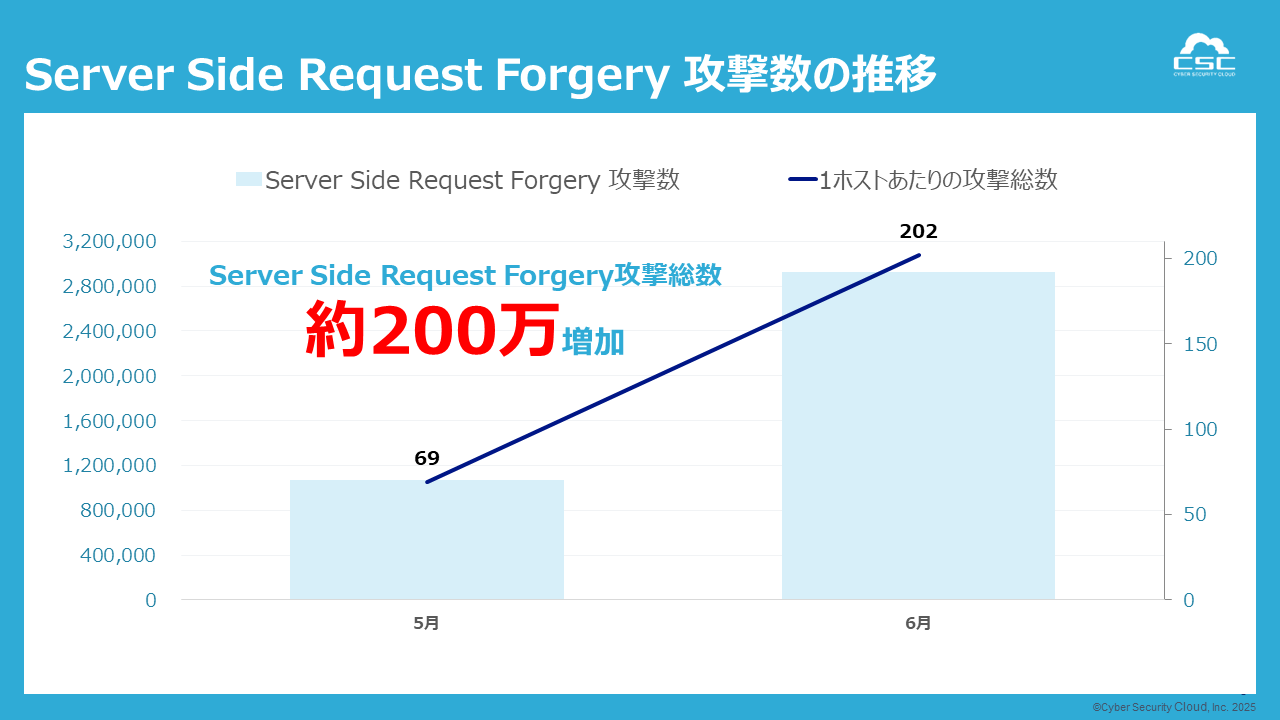
2025年6月のServer Side Request Forgery検知件数は、前月5月から約200万件増加しています。Server Side Request Forgery(サーバサイドリクエストフォージェリ)とは、サーバが本来アクセスしてはいけない場所や意図しないリソースへ、攻撃者がリクエストを送らせる攻撃手法です。
APIゲートウェイやクラウドIMDS経由での内部アクセスが狙われ、境界外から内部資源への踏み台となる危険性が高まっていると考えられます。
Server Side Request Forgeryは、件数・構成比ともに顕著な増加傾向を示しており、攻撃は主にAPIやクラウド連携の経路を狙って行われています。これにより、境界防御を回避して内部資源へ直接攻撃を仕掛けることが可能となる点が大きな脅威です。
対策としては、WAFによるServer Side Request Forgery検知ルールの適用、アウトバウンド通信(egress)の制御、クラウドメタデータサービスの保護が重要です。また、アプリケーション改修前であっても、仮想パッチ(例:WAFルールによるアクセス遮断や、不正なURLスキームを含むリクエストのブロック)を適用することで、即日リスク軽減を実現することが可能です。
■攻撃元国
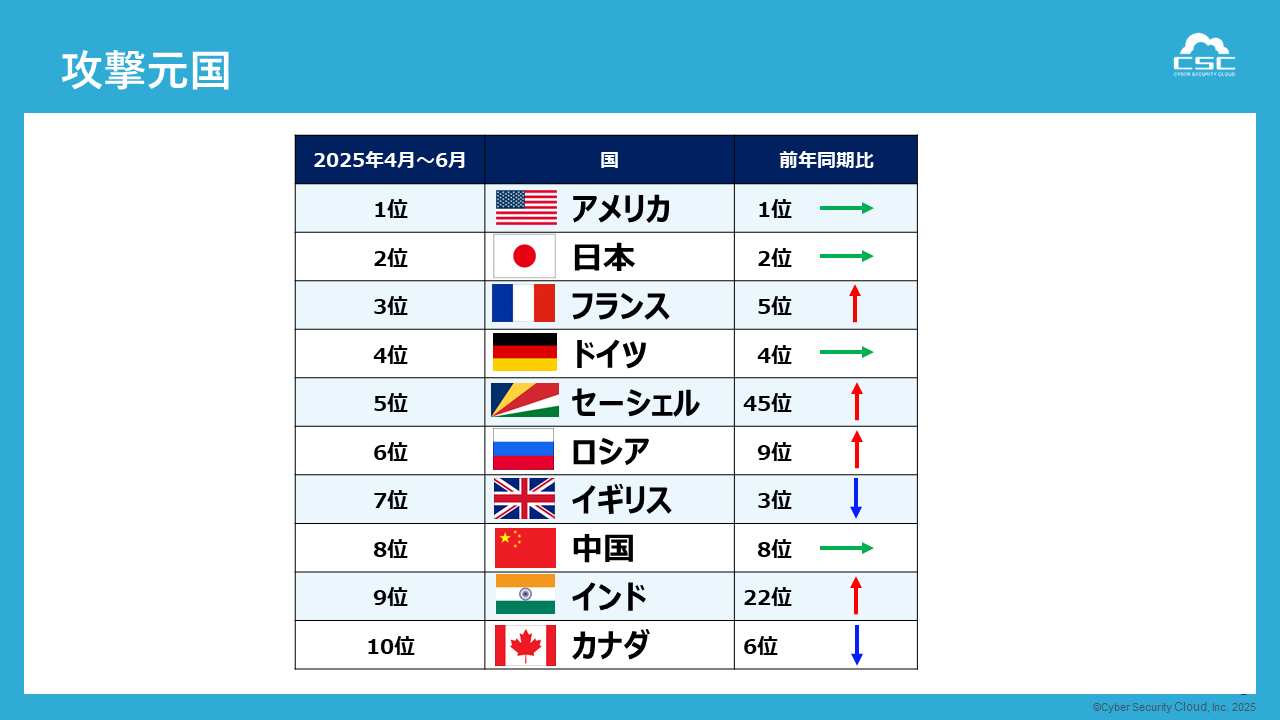
検知された攻撃元を国別に2024年同期比でみると、攻撃件数の上位は1位アメリカ、2位日本、3位フランス、ドイツと続きました。
上位国についてはさほど変化はありませんが、2024年4月〜6月で45位だったセーシェルが、今回の調査で5位に順位を大きく上げています。
■最も狙われた日は5/25(1,029万件)/5月後半に連日の“1000万件級”
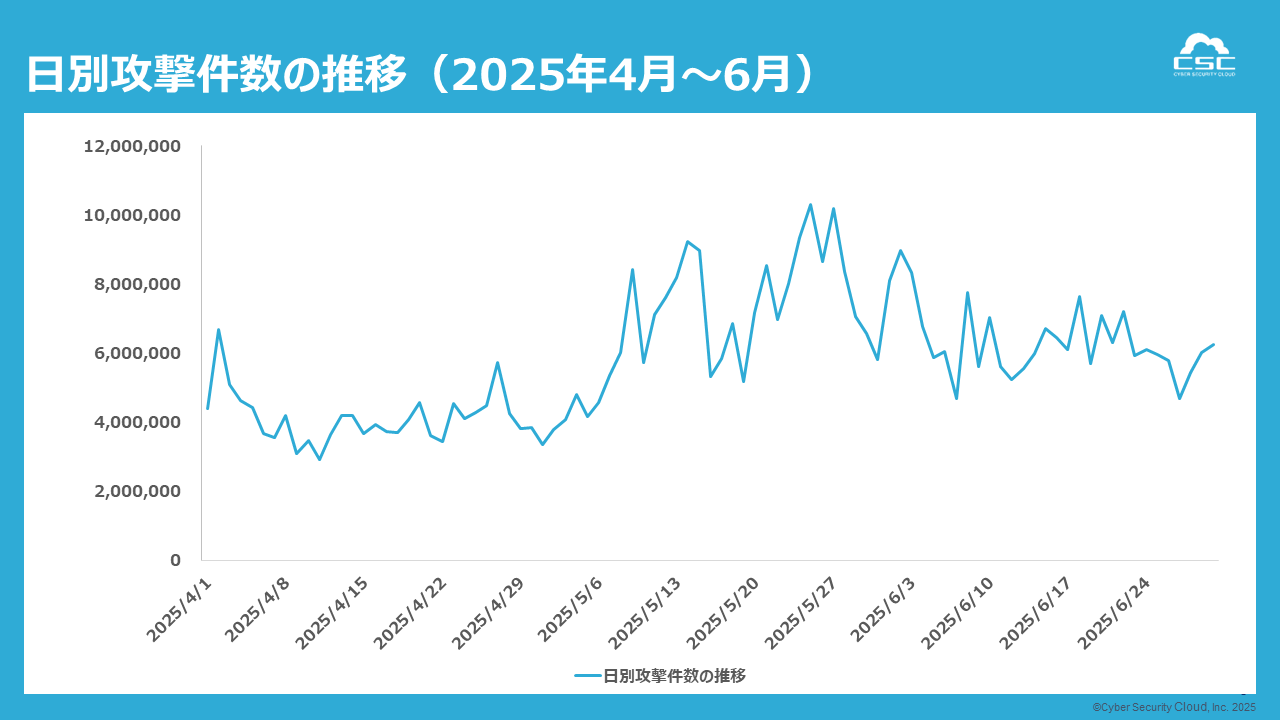
2025年5月後半、攻撃トラフィックは一気に加速しました。ピークは5月25日の1,029万件で月間最多を記録し、この日を皮切りに27日にも1,018万件と“1000万件級”が立て続けに観測されました。5月後半全体で平均約810万件と前半を大きく上回り、2025年で最も狙われた期間となりました。
これらの急増は、ボットネットを用いた自動スキャン型攻撃や、分散型サービス妨害(DoS/DDoS)攻撃の前兆である可能性が高いと考えられます。一定の条件を満たした対象に対して短期間に一斉アクセスを試みる動きが見られ、インフラ負荷や情報収集を目的とした行為が推察されます。
■4月~6月に攻撃が増加する要因
4月~6月は、運用体制・変更イベント・情報露出が同時多発的に重なる構造的にリスクが高い四半期です。当社の観測・分析から、以下の要因が複合的に作用していると考えられます。
長期休暇・連休の影響(監視の薄さ × 攻撃の活発化)
4〜5月は各地域で大型連休が重なり、運用監視や初動対応が相対的に手薄になりがちです。偵察(Webスキャン/Blacklisted UA)から実行段階(SQLi/SSRF等)への移行が活発化し、5月後半〜6月初旬にピークが立ちやすい傾向が当社観測でも繰り返し確認されています。
年初〜2Qの「新規公開・構成変更」の集中
新年度・新予算の反映に伴い、新規サイトや新機能の公開、インフラ切替が4月~6月に集中。初期設定ミスや既知CVEの取りこぼしが発生しやすく、当社の検知でもSpring系/SQLiは月末に強く、Traversalは月初に強いなど、リリース/調整タイミングと親和するパターンが見られます。
脆弱性公開・PoC露出の時期的偏り
春〜初夏はイベントや研究発表が重なり、脆弱性公開直後のスキャン波が発生しやすい季節です。6月上旬の実行系スパイクはその典型で、一方で個別CVE(KEV等)との“同日相関”は強くなく、「露出増 × スキャンの一般化」により横断的に探索が拡散している可能性があります。
CMS/プラグイン/フレームワークの更新タイミング
WordPressやPHPUnit、Spring/Tomcatなどエコシステムの更新に伴い、その周辺を狙うスキャンが4月~6月に偏るケースがあります。実データでもPHPUnit/WordPress/SSRF/ServerSideCode関連の検知が上位に定着しています。
以上を総合すると、4〜6月は「連休による監視の手薄化」「変更イベントの集中」「脆弱性情報の露出増」が重なり、短期間に高強度のスパイクが発生しやすい四半期といえます。対策として、連休前後のハードニング、月末の変更ゲーティング強化、公開直後の追加モニタリングを徹底し、件数だけでなく攻撃率で評価することが重要です。
■ 株式会社サイバーセキュリティクラウド 代表取締役CTO 渡辺 洋司からのコメント
今回の結果は、2Qに特有の構造的リスクが数値として可視化されたものと受け止めています。5月後半のスパイクは、連休期の監視体制の薄まり、月末の変更集中、脆弱性情報の露出に、自動化された探索とスキャンの一般化が重なったことが背景にあると考えられます。
また、SSRFの急増は、APIやクラウド連携が内部資産への入口となり得るリスクを改めて浮き彫りにしました。あわせて、SQLiやXSSなどの従来型攻撃も引き続き高水準で観測されています。
これらを踏まえると、WAFでのSSRF検知適用、アウトバウンド通信管理やIMDS保護、公開直後の追加モニタリング、月末の変更ガバナンス強化など、運用実態に即した対策の組み合わせが有効と考えます。また、件数だけでなく攻撃率に基づく評価や、ゼロデイ露出時の仮想パッチによる暫定対応から恒久対策への移行を通じて、スパイクの影響低減が期待できます。
当社は、実データに基づく知見の提供と製品機能のアップデートを継続し、安心・安全なWeb運用を支えてまいります。
■株式会社サイバーセキュリティクラウドについて
会社名:株式会社サイバーセキュリティクラウド
所在地:〒141-0021 東京都品川区上大崎3-1-1 JR東急目黒ビル13階
代表者:代表取締役社長 兼 CEO 小池敏弘
設立:2010年8月
URL:https://www.cscloud.co.jp
「世界中の人々が安心安全に使えるサイバー空間を創造する」をミッションに掲げ、世界有数のサイバー脅威インテリジェンスを駆使したWebアプリケーションのセキュリティサービスを軸に、脆弱性情報収集・管理ツールやクラウド環境のフルマネージドセキュリティサービスを提供している日本発のセキュリティメーカーです。私たちはサイバーセキュリティにおけるグローバルカンパニーの1つとして、サイバーセキュリティに関する社会課題を解決し、社会への付加価値提供に貢献してまいります。
