ニュース
株式会社サイバーセキュリティクラウド(本社:東京都渋谷区、代表取締役:大野 暉、以下「サイバーセキュリティクラウド」)は当社が提供しているクラウド型WAF「攻撃遮断くん」で観測されたサイバー攻撃の状況から年末年始休暇における対策をまとめました。
本レポートを公開することで、企業に対してサイバーセキュリティに関する意識喚起を行ってまいります。
■目次:
①はじめに
②長期休暇のサイバー攻撃状況
②休暇前の対策
③休暇後の対策
④おわりに(総括)
■はじめに:
長期休暇(年末年始、GW、夏季休暇)においては、システム管理者に加えて外部ベンダーの担当者なども長期間不在となり、通常時とは違いサイバー攻撃による被害が発生した場合、長期化する可能性があります。本プレスリリースではクラウド型WAF「攻撃遮断くん」のデータより、長期休暇の状況を注意喚起するものとなります。
-調査対象期間:2017年12月1日(金)~2018年1月31日(水)
-調査対象:「攻撃遮断くん」をご利用中のユーザーアカウント
-調査方法:「攻撃遮断くん」で観測した攻撃ログの分析
■長期休暇のサイバー攻撃状況
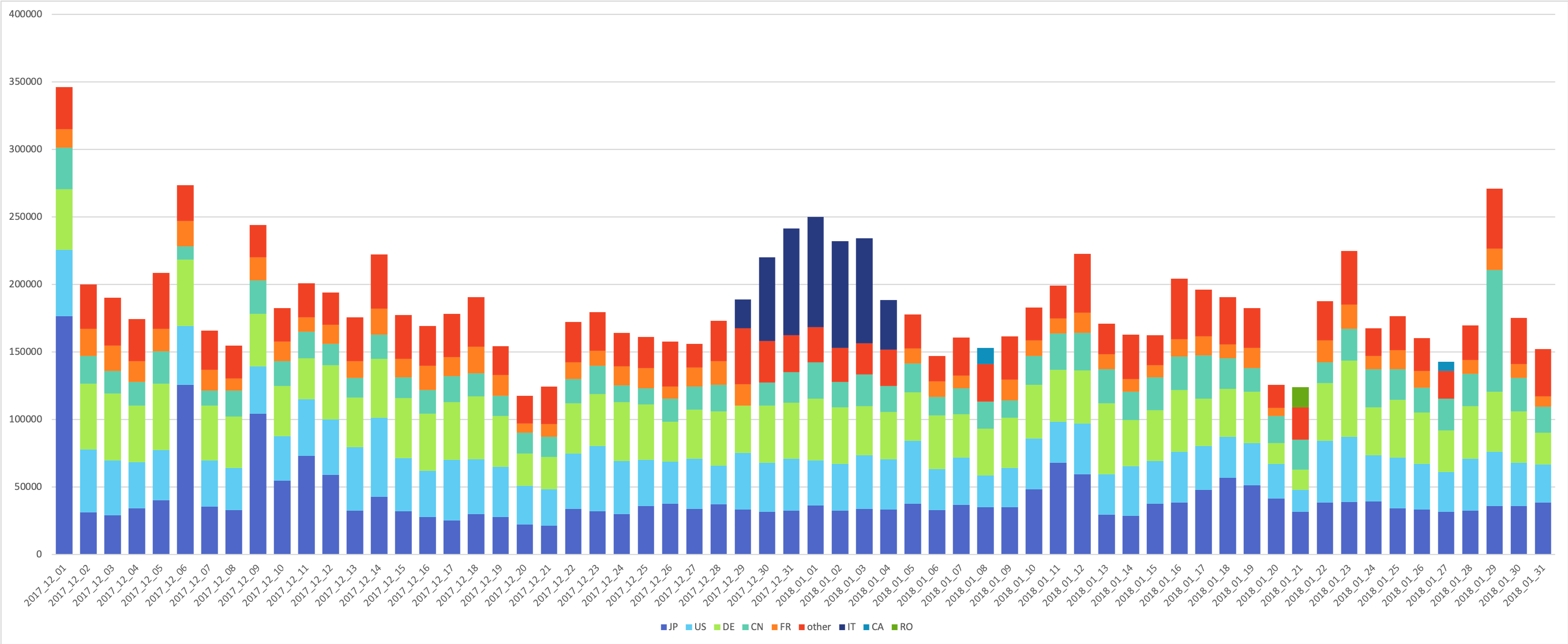
① 2017年12月1日〜2018年1月31日 攻撃検知数推移(攻撃元国別)
2017年〜2018年の年末年始における攻撃検知の状況は上記図の通りです。
12月1日に35万件近い攻撃の検知が見受けられたのち、12月のほとんどが20万件以下の検知数であることがわかります。12月の後半に差し掛かるところで、攻撃検知数が上昇しています。2017年12月28日を皮切りに上昇、2018年1月1日に山場を迎え、緩やかに減少しています。日本での一般的な年末年始休暇は2017年12月29日〜2018年1月3日となりますが、その前後数日を含め攻撃の対象となっていたと言えます。
このことから、年末年始の期間はサイバー攻撃の被害を受ける可能性が高いことがわかります。
上記期間で攻撃検知の多い国のトップ5は、アメリカ(US)、日本(JP)、中国(CN)、ドイツ(DE)、フランス(FR)となっていますが、2017年12月29日〜2018年1月4日の期間でのみ、イタリア(IT)からの攻撃が多く検知されていることがわかります。
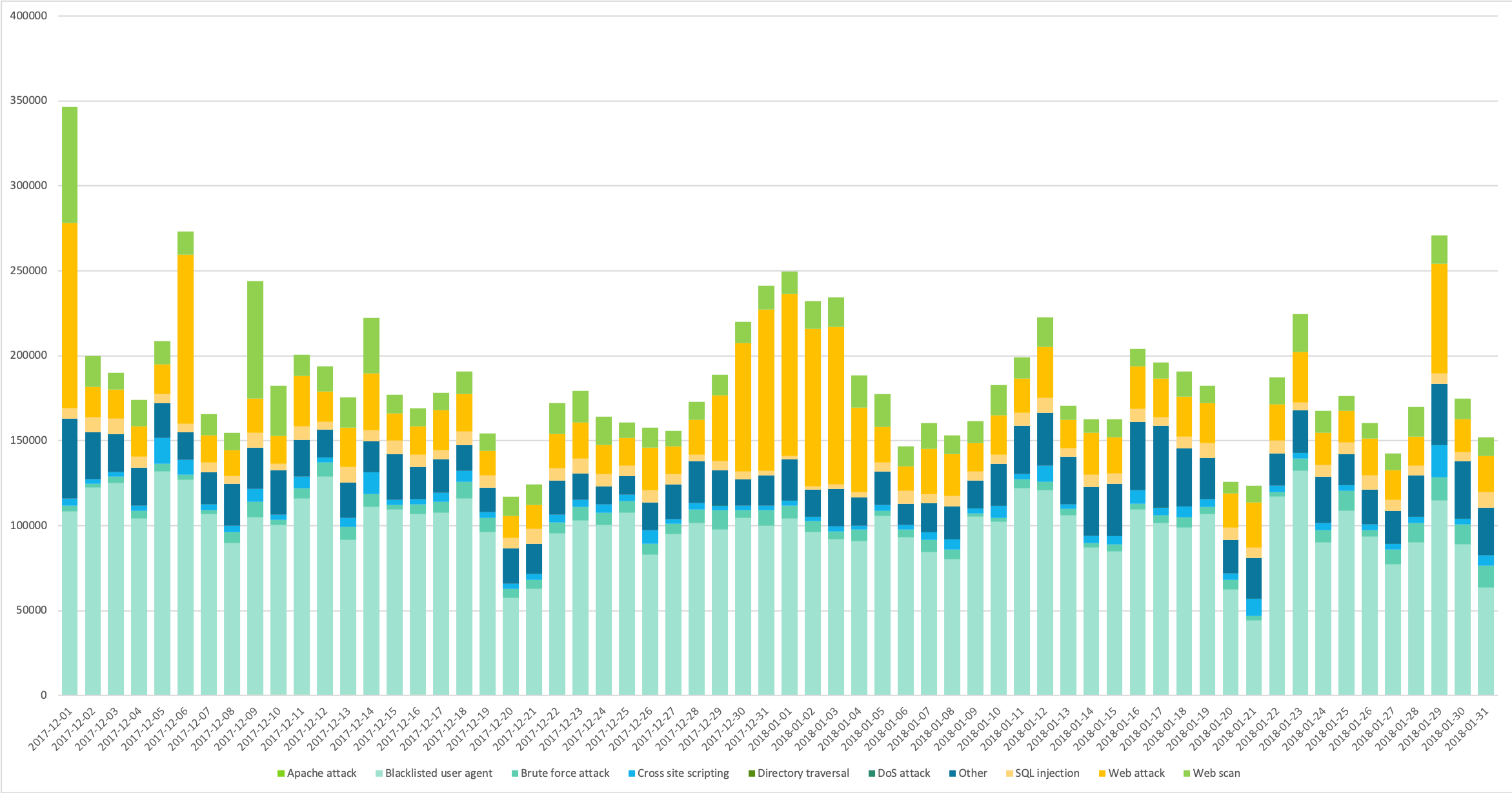
② 2017年12月1日〜2018年1月31日 攻撃検知数推移(攻撃種類別)
攻撃種別で見ると、「Blacklisted user agent」に分類される攻撃が1日あたりの攻撃検知数の半分ほどを占めています。他の期間では1日の割合の中では比較的低めの数値で検出されている「Web attack」が2017年12月28日〜2018年1月5日の期間で増加しています。
これらの事柄から、年末年始のような長期休暇中にはサイバー攻撃に対する対策を実施しておくことが重要であることがわかります。
最悪の事態を防ぐためにも以下の対策を実施することを心がけましょう。
<攻撃概要>
1.Blacklisted user agent
脆弱性スキャンツールを利用したBotによる攻撃です。
「ZmEu」「Nikto」「Morfeus」などといったスキャンツールが該当します。
2.WEBアタック
WEBアタックはDoS攻撃に近い攻撃やOSコマンドインジェクションを行う攻撃です。
3.WEBスキャン
WEBスキャンは攻撃の対象を探索する動作や、無作為に行われる単純な攻撃で脆弱性を探す攻撃予兆です。
4.ブルートフォースアタック
ブルートフォースアタックは暗号解読やパスワードを割り出すために総当たりで攻撃するものです。
5.SQLインジェクション
SQLインジェクションはwebアプリケーションの脆弱性を利用し、アプリケーションが想定して
ないSQL文を実行させることで、DBを不正に操作する攻撃です。
6.クロスサイトスクリプティング
クロスサイトスクリプティングは攻撃者が作成したスクリプトを脆弱性のあるWEBサイトを利用し
閲覧者に実行させる攻撃です。
7.ディレクトリトラバーサル
ディレクトリトラバーサルはWEBサーバ上のファイルに不正アクセスする攻撃です。
8.その他
各種OSやミドルウェアなどの脆弱性を突いた攻撃をその他としております。
通常、WAFの範囲外とされるものなども含みます。
WebサイトないしWebアプリケーションを経由しない攻撃です。
■休暇前の対策:
①緊急時の連絡体制・連絡先の確認
万が一不測の事態が発生した場合を考慮し、緊急時の連絡体制や対応手順等を確認してください。これは、自社はもちろん、外注などの委託先企業を含めた外部の企業との連携も含みます。
休暇中に担当者が海外旅行に行っていて連絡が取れないといった事態を防ぐためにも、休暇中の各メンバーの所在を明らかにしておく必要があります。また、深刻なインシデントの発生や、利用しているシステムに脆弱性が発見された場合でもスムーズに対応ができるように、連絡フローや決裁権の所在を整備しておきましょう。また、緊急連絡先に変更がないかの確認も行なってください。
②使用しない機器の電源をOFFにする
長期休暇中に使用しない機器は全て電源をOFFにするのが望ましいです。
特にサーバなどは何かあってからでは遅いので、OFFにできるものはなるべく電源を切りましょう。
③重要データのバックアップデータを取得する
不測の事態が発生した場合に備え、データのバックアップを取っておきましょう。
④サーバのOSやソフトウェアなどに最新のセキュリティパッチが適用されていることを確認する
サーバだけでなく、社員が使用する機器も最新の状態になっているかを確認しましょう。
■休暇後の対策:
休暇後の対策としては、サービスの停止や改ざん等の目に見える事故が起こらなかった場合でも、万が一のことを考慮して、サーバに対する不審なアクセスが発生していないか、システムログ、アクセスログ等の確認の実施を推奨します。サイバー攻撃は目に見える攻撃ではない為、通常と変わらない状況と安易に判断せず、必ず確認をするようにしましょう。
■終わりに(総括):
長期休暇時であってもサイバー攻撃数が減少するわけではない為、2019年も引き続き攻撃が継続されることが予想されます。
どんな些細なことでも、常時と異なる点を発見した場合は、即座に担当者へ連絡し、状況を確認する様にするべきだと言えます。
人員が手薄になることも考慮した上で、通常時と同じように連絡し対応できる体制を構築すること、そして問題がないかを休暇後に確認することが重要になります。
■「攻撃遮断くん」について
https://www.shadan-kun.com/

「攻撃遮断くん」は、Webサイトへのサイバー攻撃を可視化・遮断するクラウド型WAFのWebセキュリティサービスです。
官公庁や金融機関をはじめ、大企業からベンチャー企業まで業種や規模を問わず様々な企業で採用され、2013年12月のサービス提供開始から約3年半で累計導入社数・累計導入サイト数 国内第1位※1を記録しています。
※ 攻撃遮断くんの名称、ロゴは、日本国における株式会社サイバーセキュリティクラウドの登録商標または商標です。
※1出典:「クラウド型WAFサービス」に関する市場調査(2017年8月25日現在)<ESP総研調べ>(2017年8月調査)
■株式会社サイバーセキュリティクラウドについて
会社名 : 株式会社サイバーセキュリティクラウド
所在地 : 〒150-0011 東京都渋谷区東3-9-19 VORT恵比寿maxim3階
代表者 : 代表取締役 大野 暉
設立 : 2010年(平成22年)8月
URL : https://www.cscloud.co.jp/
「世界中の人々が安心安全に使えるサイバー空間を創造する」この理念を掲げ、サイバーセキュリティクラウドでは、自社で一貫してWebセキュリティサービスの開発・運用・保守・販売を行っています。
これまで技術者が必須であったWebセキュリティの領域において、いち早くクラウド化することで「早く、簡単に、より安全」なWebセキュリティ対策を実現、運用負荷の劇的な改善を可能としたことが、高く評価されています。2018年10月には業界の収益(売上高)に基づく成長率のランキング、「デロイト トウシュ トーマツ リミテッド 2018年 日本テクノロジー Fast 50」において、過去3決算期の収益(売上高)に基づく成長率495.72%を記録し、10位を受賞いたしました。これからも、全ての企業様が安心安全に利用できるサービスを開発し、情報革命の推進に貢献するために私たちは挑戦し続けます。
